Dynamic Malware Analysis on an ELK Stack
Recently i begun setting up a home lab with an Elasticsearch server and a seperate vm running Windows. On the VM i had sysmon running and configured to send logs to Elasticsearch. Additionally, i setup the Elastic security and was very impressed with the level of detail the security agent collected. I then ran some malware on the vm to test the detection logic, and was very impressed with the outcome. That being so, i can see this setup to be a very good dynamic malware analysis work bench for incident responders and forensic experts.
How to set this up in a home lab for free in under 10 minutes?
Prerequisites
- You can use any virtualisation solution that you’d like, just make sure you have the ability to create snapshots. Hyper-V is a free and responsive feature built into Windows. Use whatever you’d like.
- Next, create two virtual machines. Download a clean ISO of Windows 11 from Microsoft. One VM will be your malware analysis box, the other will be used for the ELK services and used to extract telemetry.
- #Opitional – Setup your malware analysis VM. I’d suggest FLARE-VM, this is the best and quickest way to customise a vanilla Windows VM to what we need.
Step 1 – Download and setup ELK
- Download Elastic – https://www.elastic.co/downloads/elasticsearch
- Download Kibana – https://www.elastic.co/downloads/kibana
- Unzip both Kibana and Elasticsearch into a folder
- Run “bin\elasticserach.bat” make sure you do not run as admin, i.e. C:\ELK\elasticsearch-9.1.2-windows-x86_64\elasticsearch-9.1.2\bin\elasticsearch.bat
- Give the batch file about a minute to run, then it will pause and you will see something similar to the following, note the password and registration key in the console:
- Leave the elasticsearch window running, now head to Kibana.
- Run bin\kibana.bat as normal user (not run as admin). i.e. C:\ELK\kibana-9.1.2-windows-x86_64\kibana-9.1.2\bin\kibana.bat
- Leave the kibana window to run for about a minute, then you’ll see a URL with a code in the paramter at the end, i.e.
-
- Grab the URL, open a browserand visit the URL
- Copy the code in the Elasticsearch console and paste it in the web browser, then click configure elastic
- Once done, you’ll be taken to http://localhost:5601/login?next=%2F
- Don’t log in yet
- Kibana has the configuration set to the elasticsearch service using the host local ip, rather than localhost which it should be set to. We need to change this. Edit the kibana.yml file located in the config directory, i.e. C:\ELK\kibana-9.1.2-windows-x86_64\kibana-9.1.2\config\kibana.yml
- change [https://172.30.227.56:9200] to [https://127.0.0.1:9200]
- next, add the following lines to the bottom of the configuraton file:
xpack.encryptedSavedObjects.encryptionKey: “a_32+character_long_random_string_here” #this can be any 32 Char string
xpack.security.encryptionKey: “another_different_32+character_string” #this can be any 32 Char string
xpack.reporting.encryptionKey: “yet_another_different_32+character_string” #this can be any 32 Char string
- Next, save and close the kibana batch file and reopen it without running as admin. When you click the x button, it can take 5 seconds to close the services, don’t force close.
- Now you have a basic ELK (minus the L) stack.
- Next, click “explore on my own”.
- We now have ELK running, however if we restart the computer, we will need to run elasticsearch and kibana batch files seperately again. You can have these run as a service at startup, use a batch file or NSSM for this. Have a Google or ask ChatGPT for a simple guide on how to setup Kibana and Elasticsearch services.
Step 2 – Setup Fleet Server
- Next, on the left-side navigation panel, scroll down to Management > Fleet.
- http://localhost:5601/app/fleet
- Click “Add Fleet Server”, this will be the box that is running the elastic and kibana services to make it simpler. Basically endpoints will be managed by the fleet server. In deployments in large environmnents this may be a seperate server from the elasticsearch server, however we’ll just keep it the same server for simplicity.
- Name: FleetServer (can be whatever you’d like)
- URL: https://<local ip address of the fleet server>:8220
- Click “Generate Fleet Server Policy”, wait a minute.
- Perfect, now grab the Powershell command listed below and execute that on the same server that is running elasticsearch:
- You may see the following error, this is caused by the fleet install script not considering the second folder with the elastic-agent, i.e.
- So to get around this, modify the script to duplicate the CD command on line 4, i.e.:
cd elastic-agent-9.1.2-windows-x86_64
cd elastic-agent-9.1.2-windows-x86_64 - Then run again.
-
- You might get some errors in red, that is caused by files that already exist from our first run, ignore those. You will be asked to install the elastic agent as a service, type “y” and enter.
- Refresh the web browser that is pointing to the fleet agents, and you should see your new fleet agent check in. It might say status unhealthy, this will self-resolve over the coming hour.
Step 3 – Deploy Elastic Agent
- Next, we need to deploy our elastic agent to the malware analysis device.
- Click “add agent” in the fleet management screen
- Go to settings, then in the “FleetServer” hosts, edit the URL to be the local ip address of the device, not 127.0.0.1, i.e. https://172.30.227.56:8220
- Create a new policy, this will be a group that all your agents will join. We will also deploy integrations to our policy in the future which will distribute to all agents in that policy.
- Copy the install script, and open powershell ise as local admin as we will need to make some changes to the script:
- Add “–force –insecure” to the end of the final line.
- Run this and let it complete, it may take a few minutes to check in and become healthy.
- You’ll notice in the Fleet management server page, the new device has checked in. We’re almost done now, we just need to enable certain integrations to the fleet policy.
Step 4 – Add Integrations
- Head to Management > Integrations and type “defend”. The first item is Elastic Defend, select this.
- Next, select “Add Elastic Defend”
- Give the inegration a name, maybe “defend” or similar.
- Scroll down, and make sure you click “Existing hosts” then select the policy we have for malware analysis.
- Click save and continue.
- Duplicate this process and install the following integrations to the fleet:
– Threat Intelligence Utilities
– Windows
– Prebuilt Security Detection Rules - After doing the above steps, you now have a working Elastic Defend environment.
Step 5 – Enable out-of-the-box Detection Rules
- Next, we’ll begin to enable some in-built detection rules and correlation logic in the security agent.
- Head to Security > Manage
- On the left hand side, select “Rules”
- Select “Detection Rules”
- Next, select, “Add Elastic Rules” near the top, it should show a number like 1375:
- http://localhost:5601/app/security/rules/add_rules
- You have two options at this point, either use the tags to filter the types of rules you can enable – remembet there is 1,375 rules, so you may exclude some important ones accidently. Otherwise, you can just enable all rules. Remember this server is only going to be used for malware analysis, so although the potential load in an enterprise environment would be very high, in a malware sandbox this will be suffient.
- I’ll enable all 1,375 rules by selecting the “Install all” button
-
-
- Give it a few minutes to download and install all rules. Don’t refresh or move the page – grab a coffee
Considerations
- At this point, we now have a very verbose SIEM and EDR. Any action that is made on the device that has an installed agent will cause a lot of alerts and will record very detailed telemetry.
- We now have a sandbox setup and ready to use. Snapshot your VM as this is a clean state.
- Whenever you detonate malware locally, consider network isolation so that your local devices are not at risk.
- Some notes on having used this for malware analysis.
– when i restore a clean snapshot, i always double check that the agent checks in correctly to the fleet server
– After i bring the malware over, or am ready to browse to a site and download it, i will create a file or folder with a certain unique tag. This might be date, time, or case number. e.g. “test123-vbs-downloader”. This means that after i create that file or folder, i will immediatly execute the malware (within a second or so). Then when i track the activity of the malware, i can use the file or folder that i made as a time reference point for easy filtering. Basically anything after that file or folder was created is considered suspicious or relevant to the malware.
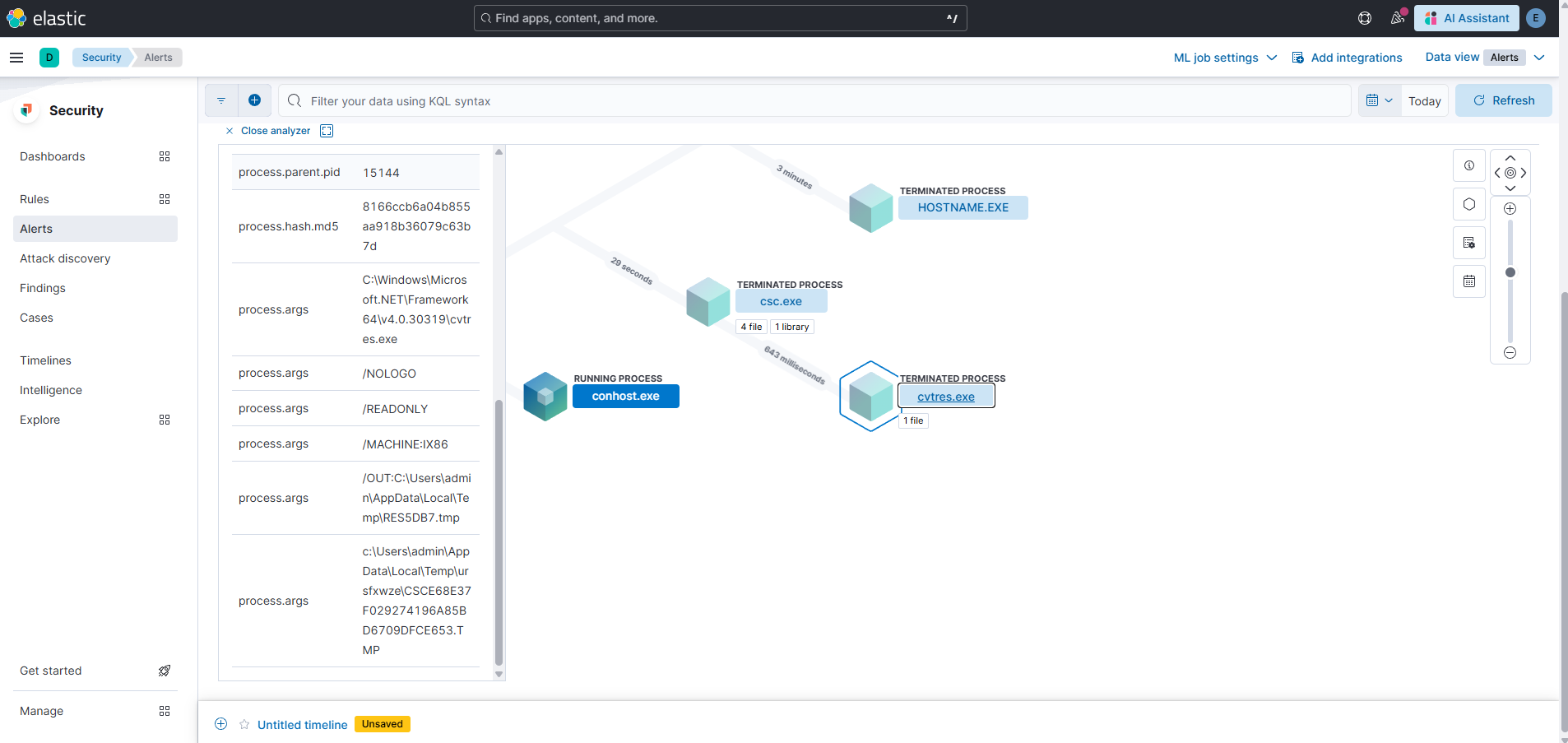
Screenshots
Some screenshots of running malware samples are included below:

